
Explore the Case Study
Dive into our latest case study to uncover how Axi transformed its real estate strategy with Cyberseer's expertise.
The threat landscape is continually evolving affecting all types of businesses that embrace and rely on technology to continue their day-to-day operations.
The explosion of cloud-based applications and services coupled with initiatives such as Bring Your Own Device (BYOD) present significant security challenges to the IT Security Department and keep many CISOs awake at night.
The below graphic has never had more accurate than in today’s digital, always-on world.
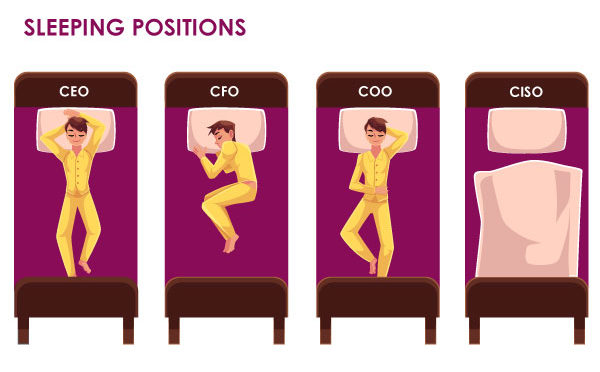 What are the concerns that contribute to making the role of a CISO almost untenable?
What are the concerns that contribute to making the role of a CISO almost untenable?Here are 8 critical reasons supporting why utilising an MSSP can empower your security operations with the people, processes and technology required to take control and reduce dwell time to a minimum for your organisation.
Help ensure your CISO gets some rest and you don’t suffer the consequences of a damaging cyber breach:
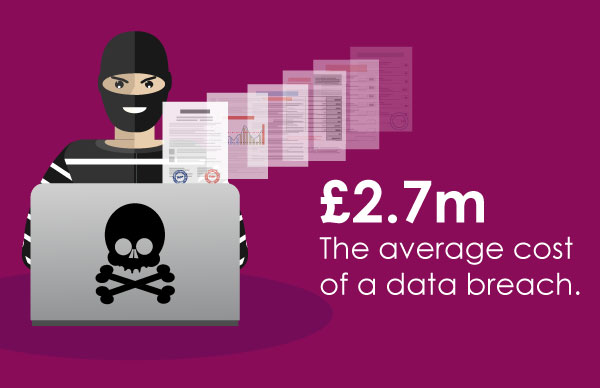 (Ponemon Institute, 2017 Cost of Data Breach Study).
(Ponemon Institute, 2017 Cost of Data Breach Study).
Immediate disruption is significant! Nearly one-third of data breaches suffered by companies around the world have resulted in someone losing their job, according to a 2018 Kaspersky Lab study.
Not to mention the reputational damage, loss of competitive advantage, erosion of customer confidence, plus higher insurance premiums and regulatory fines.
With the rising costs of a cyber-attack, it’s now a boardroom concern.
Utilising an MSSP to proactively monitor your enterprise can help thwart and thus significantly reduce the impact of any attacks targeting your enterprise, be it from internal or external sources.
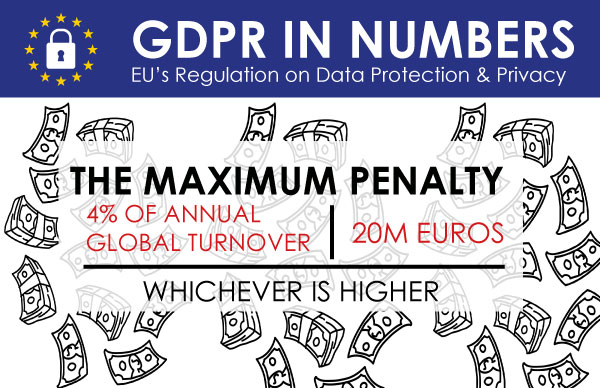
With the introduction of the EU’s General Data Protection Regulation (GDPR), it’s vital for businesses to pay even closer attention to their data protection strategies.
Organisations are at risk of significant fines if they fail to demonstrate appropriate controls and/or fail to report security breaches to a relevant authority within 72 hours.
To execute notifications of data breaches, organisations must invest in a holistic cybersecurity program.
The need for improved visibility of data and the capability to detect, respond and report breaches is now greater than ever.
An MSSP enables your organisation to align with the control mandates within GDPR and ensure that the risk of financial penalties is reduced significantly.
It’s important for appropriate controls, such as behaviour-based security solutions to be deployed to accurately detect and respond to attacks before they cause significant damage to your assets and affect your reputation.
Cyberseer utilises behaviour-based endpoint monitoring technology and machine learning to surface anomalous activity swiftly.
(Department for Digital, Culture, Media and Sport, Cyber Security Breaches Survey 2019: Statistical Release).
The threat of a cyber-attack is widespread and real in the UK. It’s now a case of "when", not "if" you’ll be targeted. Cybersecurity and how to protect the business are priority issues.
Cyberseer can challenge and improve your security strategy, protecting your organisation’s assets, customer data and third-parties integrations from compromise.
As more and more organisations adopt software as a service and cloud-first initiatives, attackers are following the data.
As a result; Attacks against cloud providers, telecoms, and other organisations with access to large amounts of data have increased.
Cyberseer solutions incorporate log data from your cloud deployments/applications and profile this data alongside your traditional on-premise log data ensuring that complete visibility of your enterprise end-to-end is achieved irrespective of its location.
 (Cybersecurity Ventures, Cybersecurity Job Report 2018-2021).
(Cybersecurity Ventures, Cybersecurity Job Report 2018-2021).
There is a critical talent shortage, and this alone can be a challenge. With a current cybersecurity skills shortage of 2.9 million employees, it’s no wonder that cybersecurity salaries continue to rise.
Utilising an MSSP can help to reduce operational risk as well as ensure an unfilled vacancy doesn’t affect your front-line defences.
Cyberseer’s approach involves hiring and retaining Tier 3 Forensic Analysts as part of our managed security service team.
Modern cybersecurity programs are costly to build. It can be expensive to invest in the best-in-class cybersecurity tools alongside costs for the training required for staff to use the new tools.
MSSPs enable organisations to replace large, capital expenditures associated with this investment with predictable, fixed ongoing operational costs.
Cyberseer adopts a ‘do more with less’ approach utilising next-generation technologies to reduce alert fatigue whilst embracing industry-leading forensic analysts to threat hunt, triage and investigate; all encapsulated within an easy-to-understand user-based license model inclusive of unlimited logging.
Providing the capability to effectively monitor your enterprise around the clock can become a costly exercise. As a result, many organisations have yielded on this in favour of a 9x5 approach to monitoring.
This presents potential security as adversaries can attack at any time and are not considerate of your active monitoring hours.
Cyberseer provides a 24 x 7 priority threat alerting service as part of the deployed capability.
This service autonomously notifies our analysts of anomalous activity and the Cyberseer enrichment engine starts building up threat intelligence information against individual events within the user or entity timeline to save the analyst time collecting and verifying the data.
This greatly improves the ‘Time to Respond’ (TTR) metrics as well as controlling the volume of human effort that’s required to triage each threat with the same level of accuracy.
Superior protection:
with access to the brightest minds and security expertise.
24/7 threat monitoring & alerting.
access to the best-in-class cybersecurity technology.
Focus in business;
Cost savings;
Peace of mind;
Virtual extension of your IT Security team who are on hand to support you.
Superior protection.
Many factors affect the ability of an organisation to remain secure, including an exponential increase in log data due to the adoption of cloud operating models, endpoint monitoring and more reliance being placed on online applications.
The need to ensure that your team are fully up to date on the latest threat-hunting techniques, cyber exploits and vulnerabilities is critical.
To help put this challenge into perspective; it’s been estimated that 90% of all log data globally was generated within the last 24 months.
Utilising this log data effectively to your advantage and identifying malicious activity early is your biggest challenge and best defence against a damaging cyber-attack.
Cyberseer utilises Machine learning technologies from leading security vendors combined with automation and orchestration from Cyberseer’s ASPECT platform (Automated Security Platform Enriching Cyber Threats).
ASPECT enhances and contextualises data and alerts that are notified from monitored devices.
To achieve this ASPECT can continually automate and orchestrate security data to provide an enriched contextualised view of security alerts and associated intelligence that enable our analysts to quickly identify and manage threats for your organisation.
The utilisation of ASPECT and our dedicated forensic analysts ensures that, as greater reliance on cloud technologies and disparate operating models becomes more complex, the increased data volumes generated as a result don’t create gaps in visibility.
Sources: Cyber Security Breaches Survey 2019 | Cyber Security Ventures

Dive into our latest case study to uncover how Axi transformed its real estate strategy with Cyberseer's expertise.