Introduction:
At Cyberseer, we pride ourselves on staying ahead of the curve when it comes to spotting and stopping threats before they wreak havoc on our client's systems. In this blog post, we delve into a recent incident where our vigilant monitoring uncovered suspicious activities, highlighting our methodology and the value it brings to our clients.Detecting Anomalous User Logins:
At 4 am an analyst was alerted to a priority threat flagged by Cyberseer’s ASPECT customer threat escalation platform. The alert was triggered by a behavioural anomaly in a customer environment relating to a “First Time Login & File Activity” from a suspect source. This anomaly was further reinforced using the customer’s integrated Microsoft Defender logs. Using OSINT (Open-Source Intelligence), the analyst investigated the source IP of the user actions, revealing that the login activity and subsequent file read events were attributed to a Moscow-based hosting provider. The user’s timeline of actions proceeding the 04:10 initial “Indicator of Compromise” were reviewed and highlighted further login attempts from a range of cloud providers, email rule manipulation and file read and write events from IPs not matching that of the genuine user’s normal behaviour. These malicious indicators lead the analyst to promptly notify the client via agreed priority escalation channels, providing verbal and written details of the suspected compromised accounts, and alerting them to the potential threat of data loss or lateral movement.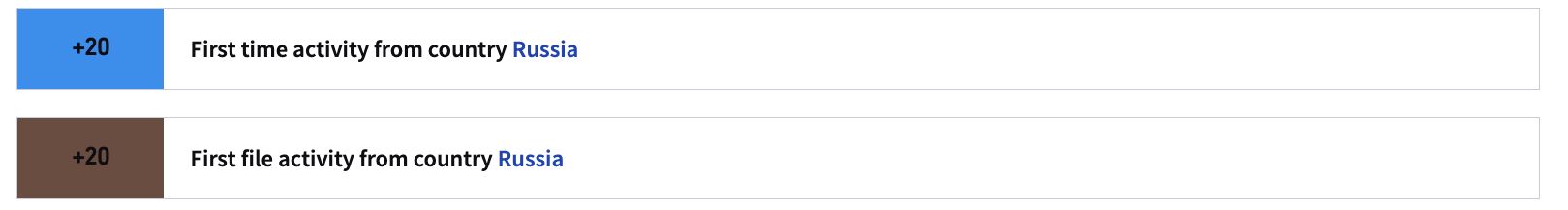
Confirmation of Compromise:
After confirming the threat and discussing the necessary actions with the customer, the analyst continued to review the post-compromise timeline of events. Upon closer examination, it became evident that one user account, holding a management role, was observed engaging in unauthorised activities, including the creation of a OneDrive folder in the user’s directory – a potential indication of illicit access. Two distinct motives were highlighted for this action, each presenting its own set of risks:
Two distinct motives were highlighted for this action, each presenting its own set of risks:
- Weaponising the Folder:
One plausible scenario is that the malicious actors intended to exploit the OneDrive folder as a conduit for delivering malicious payloads onto the compromised host. This could have allowed them to evade traditional antivirus measures on the user's host, and establish persistence on the network or extract credentials via the dropped payload.
- Data Exfiltration:
Alternatively, the OneDrive folder could have served as a clandestine repository for stolen data. In this scenario, the attackers could have exfiltrated sensitive information from the compromised environment and stored it within the folder for subsequent retrieval. The ease of sharing OneDrive folders would facilitate seamless communication between the adversaries, enabling them to siphon off valuable data, potentially blending in with Business as Usual (BAU) actions.






